Inspecting HEX Data with Fiddler Everywhere

Summarize with AI:
Capture, inspect and analyze hexadecimal data with Fiddler Everywhere. Let’s take a look!
You’re already familiar with Fiddler Everywhere from Progress Telerik and its powerful proxying capabilities. By capturing HTTP(S) traffic, the application enables you to delve into the data with sophisticated inspection and manipulation tools. This goes beyond simply observing the HTTP sessions. You can actively fiddle with the data, opening up various possibilities for using Fiddler in multiple tasks.
While we won’t go into listing all of its features today (if you’re interested in learning more, I recommend checking out this excellent blog post by Simona Yaneva), I want to highlight one of its hidden gems: the HEX Inspectors, which offer the ability to interact with raw hexadecimal data.
The Inspectors in Fiddler Everywhere
Fiddler Everywhere provides inspectors crucial in visualizing and structuring captured information from HTTP(S), WebSocket and gRPC sessions. These inspectors serve as UI tools, enabling users to analyze the content of each session through various contextual interfaces. Whether HTTP(S) traffic or WebSocket/gRPC channels, Fiddler offers contextual inspectors to delve into the captured data.
When capturing HTTP(S) traffic, Fiddler presents inspectors for different aspects such as raw HTTP headers, cookies, raw data, preview and HTTP bodies. These inspectors help users gain insights into the specific details of the captured sessions. In the case of WebSocket or gRPC channels, Fiddler goes a step further by providing additional inspectors tailored for WebSocket/gRPC metadata and individual message analysis.
It’s important to note that the data exchanged between client applications and servers may not always be human-readable. While a significant portion of the data is text-based (encrypted but decryptable when Fiddler acts as a MITM TLS proxy), instances where graphical data (for example, images and icons) or specific encoding formats are used. Additionally, some sessions may involve the transfer of binary data that requires processing by the client or server.
Fiddler’s inspectors intelligently detect the format used in each session, allowing users to load the most relevant inspector seamlessly. By simply double-clicking on a captured session, Fiddler Everywhere automatically selects the proper inspector to display the request and response of that session. For instance, if a session contains an SVG image, the Preview inspector will be loaded with a double-click, while a session with a JSON file will activate the JSON Body inspector. This cognitive interface empowers users to quickly analyze received data without worrying about its specific format.
The Hex Inspector
The HEX inspector allows you to analyze fundamental binary data that constitutes the HTTP Request/Response bodies or the WebSocket/gRPC messages. With a HEX inspector, a user can see or edit the raw and exact contents of a body/message, as opposed to the interpretation of the same content that other, higher-level application software may associate with the file format (like an image previewer or a browser that interprets HTML).
One of the most common scenarios to use the HEX inspector is to analyze data corrupted during the client-to-server connection or by system or application program problems.
The data represented in the inspector shows an offset column, followed by a column that holds the raw hexadecimal values, followed by one group of ASCII characters corresponding to each pair of hex values (each byte). Non-printable ASCII characters (like Bell) and characters that will take more than one character space (like tab) are represented by a dot (.) in the following ASCII field.
Playtime with gRPC Messages and the HEX Inspector
Let’s demonstrate how Fiddler’s HEX inspector works in real-life scenarios. We will use this gRPC demo written in Python to spice things up. To run the Python demo, you must install pip, grpcio and grpcio-tools. Once the tools are installed, you can clone the gRPC demo.
# Clone the repository to get the example code:
$ git clone -b v1.55.0 --depth 1 --shallow-submodules https://github.com/grpc/grpc Now, open Fiddler Everywhere and use the Terminal option to start two separate terminal instances. We need two instances to run the gRPC server and the gRPC client. The preconfigured terminal instance is automatically configured to go through the Fiddler Everywhere proxy, so you won’t have to set Fiddler as a system proxy.
In the first Fiddler terminal instance, start the gRPC server:
# Navigate to the "hello, world" Python example for streaming gRPC:
$ cd grpc/examples/python/hellostreamingworld
$ python async_greeter_server.pyIn the second Fiddler terminal instance, start the gRPC client:
# Navigate to the "hello, world" Python example for streaming gRPC:
$ cd grpc/examples/python/hellostreamingworld
$ python async_greeter_client.pyThe gRPC server and client are immediately streaming messages through a gRPC channel. As Fiddler is configured to capture the preconfigured terminal traffic automatically, we can start inspecting the gRPC traffic on the fly.
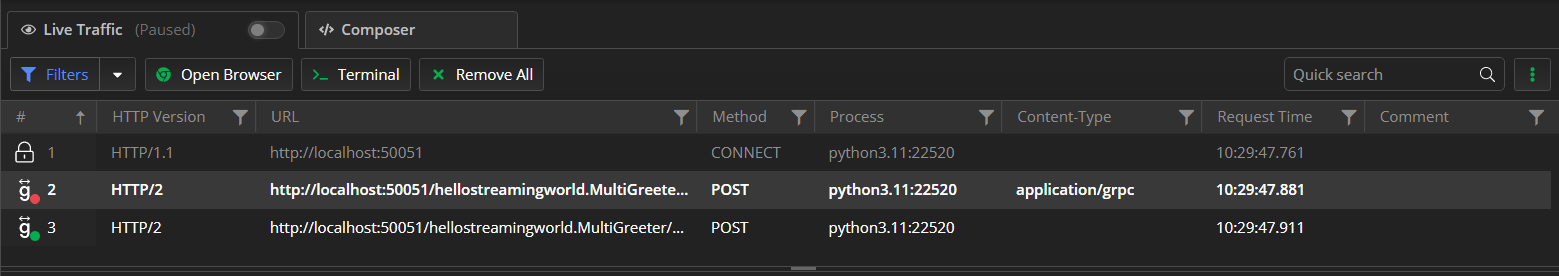
Fiddler’s live traffic grid already shows a ton of information—like that the gRPC channel was closed after all messages were streamed and that the connection utilizes HTTP/2 (gRPC is built upon HTTP/2 and won’t work if HTTP/2 support is disabled). We can see the process that generated the session, the timestamps and much more—all that from a simple glance at the live traffic grid columns.
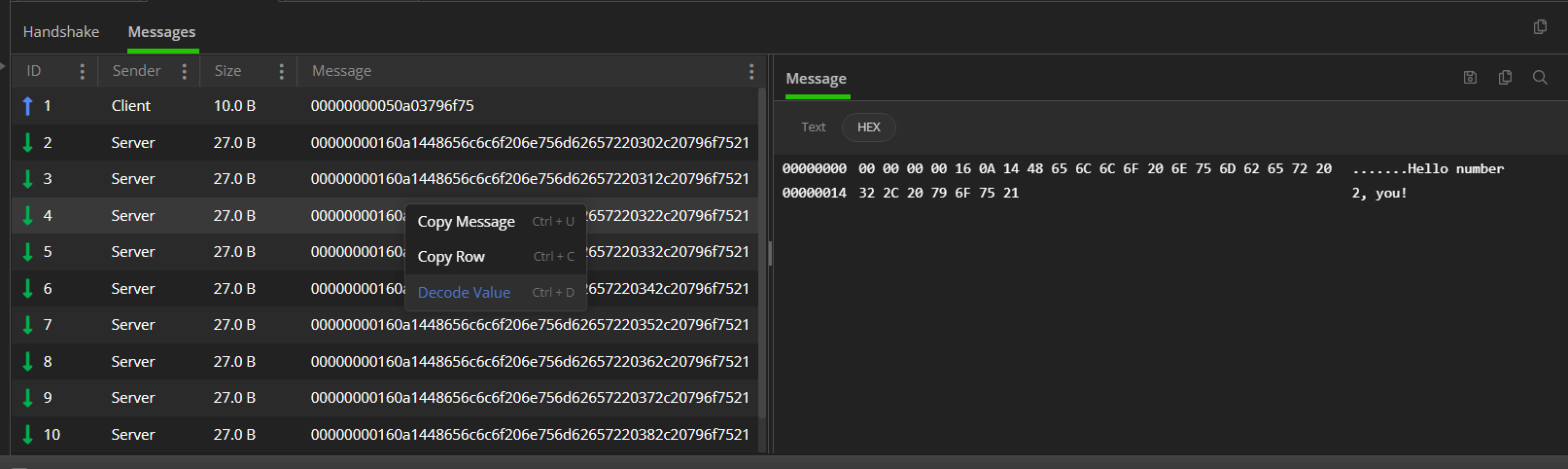
We can now move to the inspectors and focus on the Messages tab. The tab contains all streamed messages between the gRPC server and the client application. The Messages tab provides a context menu with decoding options that you can use to try to decrypt data in unreadable form.
The next step is to select a specific message we want to investigate. As a result, the message data is loaded in the Message > HEX inspector, where we can extract the needed data or quickly see a text representation of the hexadecimal content. Similarly to most hexadecimal viewers, you can save the message content to a file, keep it in the clipboard or copy/paste specific hex parts of the message.
The content that the gRPC server and clients will exchange will often be unreadable. The HEX inspector lets you make a low-level profile of the raw data transferred through the gRPC channels. Even without knowing the proto scheme (which will be the case for every gRPC application you do not own or create), the HEX inspector allows you to deep-dive and analyze captured traffic and make conclusions based on the exclusion and logical assumptions.
Wrap-up
Fiddler Everywhere already became a favorable tool for capturing and inspecting online traffic. The cognitive inspectors, the multiple proxy modes, the support for modern-day technologies—all that is just a scratch on the surface in the ocean of possibilities. Of course, the team is constantly working on adding more value, and the best way to move ahead is to share your feedback with us.
Try Fiddler Everywhere and let us know how you feel about it—we welcome you aboard!

Nikolay Iliev
Nikolay Iliev is a senior technical support engineer and, as such, is a part of the Fiddler family. He joined the support team in 2016 and has been striving to deliver customer satisfaction ever since. Nick usually rests with a console game or a sci-fi book.

-network-issues-like-a-pro-250x250.png?sfvrsn=710a0cb8_6)